#1 San Diego Cyber Security Company
Leading cybersecurity consulting services in San Diego, CA
Keep your company data secure; hire premium cybersecurity services in San Diego area.
Cybersecurity experts of Secure Networks ITC, offer proactive cybersecurity analysis, consulting, HIPPA and NIST frameworks and best cybersecurity managed services.
Call our consultant at (858) 769-5393 and protect your business against cyber threats. Anytime. Anywhere.
Proactive San Diego Cybersecurity Services
And this is not all. Our San Diego IT security experts can help with password protection, dark web monitoring, breach response, two-step authentications, limiting access to sensitive data, security patching, application security updates, DNS breach protection and much more. If your organization needs a custom approach to information security services or you are experiencing a cybersecurity incident, contact Secure Networks ITC team to help.
No Business is Immune to Cyber Attack – Deal With It!
If you think that cyber attacks happen only to enterprise companies, you are so wrong! Yes, large businesses have more data to steal but SMB is much less protected. Due to the leak of knowledge, time or budget, small business is usually an easy target for cybercriminals. Are you one of those business owners who think that there is nothing to steal from you or you believe that your employees have strong password practice? If yes, you’ll need to change your mindset. Numbers from the latest research will tell you why.43%
of SMB have been under security attack
36%
more ransomware attacks to SMB in 2021
197
days businesses need to detect a breach of data
Remember, in the cyber world, there is no such thing as the business size – it’s all about data. If you are dealing with customer’s CC information, contact info or healthcare records forget how small your business is – you have to protect sensitive data about your clients, buyers or patients no matter how big your database is. Think about your IT system as a chain that consists of links. Your servers, workstations, laptops, smartphones, printers, tablets, fax machines are those links and part of your business' IT network. As with any chain its strength and compactness depend on the weakest link. IT security specialist will make sure you don’t have weak links in your IT ecosystem and that way protect all the data that is going through your network – from a single email to a client sensitive data.
3 Steps to Protect Your Digital Assets Agianst Cyber Attacks
OR HOW WE DO ITWe like to be proactive and don’t want to wait for the attack to happen because it would probably be too late to protect 100% of your data. To offer full protection of data breach to our clients we implement several layers of protection (not just web-based) for every device you are using in the office; from small USB sticks, Android devices, Windows workstations to the servers.
San Diego Cyber Security Managed Services
Benefits of Our Cybersecurity Services
Let us create a rock-solid office network, prevent a possible attack and take care of the weakest chain in IT system.- Small business cybersecurity analysis and consulting
- Affordable Managed Cybersecurity Managed
- Dedicated small business cybersecurity consultant
- Complete solution for your network, servers and workstations
- Microsoft, Bitdefender, Cisco and VMware Partner
- Remote and on-site computer security support
- Cloud security consulting (Azure and Office 365)
- Customize your cyber protection
TALK TO SAN DIEGO CYBERSECURITY EXPERT
(858) 769-5393
Networks Security Analysis
No matter the size of your company or the industry you serve – you are at the risk of many cyber threats. Don't wait until you are the victim of a cyberattack. Defend against cyber-attacks more effectively. Let cybersecurity experts of Secure Networks ITC examine your IT network. Schedule a network audit today and talk to our consultant to safeguard your critical data.
More Services from Our San Diego Cybersecurity Company
Step-by-Step IT Security Plan
Everything from above is well documented and in alignment with your IT security plan. In this document, you will find step-by-step guidelines and procedures in a case of a cyberattack and how to mitigate the risk of a security incident. IT security plan consists of several policies you and your employees need to follow. Some policies to name are email policy, password policy, network security policy, WIFI network policy, mobile devices policy, incident response policy, etc. The plan is mandatory for some industries like medical or government. As a responsible business owner, you need to follow security standards and be an example to your employees how to understand and deal with security issues online.
Endpoint Safety: From Mobile Device to Server
Since computer and network security become so important in last decade our consulting and tech teams decided to offer the highest level of support no matter what IT plan you choose. We don’t have essential or PRO IT security services. All our security IT services are top notch and in relation to leading IT security practices. Long story short, every server, workstation or mobile device* in your office will be protected by latest anti-virus and anti-ransomware software. Your business network, VPN, WIFI or any other will have the strongest encryption almost impossible to break. And without breaking your budget! * In 2017 Android devices were more vulnerable than Windows OS devices
360° Protection 24/7
Our company name tells how crazy we are about computer security and commitment to block any sign of suspicious activities around your IT system.
HIPAA and NIST Cybersecurity Framework
With the ever-increasing problem of identity theft and overall sensitive data theft, a compliancy was set in place, which is a requirement for hospitals and companies working directly with the government. HIPAA compliance and NIST are very similar and aim to increase the overall security of the data that your system is holding. One of the easier ways of reaching compliance is going with the cloud services for all your essential apps. For example, with e-mail servers, you will have to have an anti-spam solution in place to stop malware from spreading along with a firewall to block all possible breaches to your network. With Office 365 you might not need such heavy security as it already has a lot of these measures built-in. It is very similar with other apps. For example, if you are running a hospital, you would have to have an app that would hold patient charts. That kind of app would have to be completely encrypted and protected. Going with a 3rd party vendor would be advisable.Learn more >>>

Anti-Virus Protection
Long gone are the days where you could only play it safe by visiting only a specific type of website. Malicious software has spread throughout our digital world, lurking in every corner. Your flash drive or e-mail can be compromised. Even your computer might lead you to believe that you are visiting the gmail.com website, but in fact, you are being routed to a bogus one that will steal your data. That is the reason we recommend Anti-Virus software. Many antivirus solutions have free versions and can be pretty good, but you are not searching for a good enough solution, are you? You want your computer to be protected at all times and feel comfortable in opening just about anything. Sounds like utopia? Well not exactly. Most of the top Antivirus solutions like BitDefender or Avira are pretty close to that utopia. Blocking bogus websites, cutting down the malware e-mail and eliminating virus apps from your computer.Learn more >>>
Anti-Ransomware
Ransomware is the nastiest and most evil type of malware. It encrypts your entire system and often spreads throughout your network by encrypting shared folders and servers. Once the encryption is completed, you will be asked to pay for the release of your data. Often, no matter how much you pay for it, you will never get it back. Embracing a proactive approach and installing one of many endpoints or professional versions of Anti-Virus will include Anti-Ransomware protection, delivering another layer of security. Ransomware will simply bounce off the shield in place!Learn more >>>

Biometric Security and Camera Systems
Increasing your IT security by stopping remote outside access is just a part of the overall safety of your data. Unfortunately, physical security is something that many companies overlook, believing that direct access to their system would be unlikely. The first line of defense would be installing a good camera system. Most thefts would be set off by just seeing a camera mounted on the wall and thus decreasing the chance of a breach even further. The second line of defense would be employing biometric locks for your server or even requiring a form of biometric security for computer access as well.Learn more >>>
Backup & Data Recovery
And of course, the last line of defense is a good backup. If your data gets encrypted or deleted, a backup would allow you to restore it quickly. Or even if your server gets damaged, a quick restore would decrease downtimes. As full service IT support company, Secure Networks ITC offers triple data backup and recovery services to protect what matters the most for your business. On-site, off-site and cloud backup – most advanced backup setup for the fastest data recovery.Learn more >>>


6 Cyber Security Tips for Small Businesses Owners
Before you call Secure Network ITC to help make your IT network and computer security rock solid follow simple tips from below to at least slightly improve your business’s cybersecurity.Tip #1 Train your employees
Choose one or two of your employees to learn more about the network and computer security. Send them to cybersecurity courses or buy similar courses online. After you educate them, let them introduce their knowledge to other staff in your company. Everyone in the company needs to be aware of potential risks, his/her role in case of data breach and how to protect customer information.Tip #2 Use two-step verification
A convenient way to improve and add an extra layer to security is to require two-step (two factor) verification process. In order to log in to his corporate email, PayPal, Evernote, Dropbox account, Apple, Google, etc. employees will have to type correct password and code that he/her will receive on a mobile phone as SMS.Tip #3 Enforce strong password practice
Insist on rigorous passwords. 6 characters passwords are not enough anymore. Use capital letters, symbols, and don’t use kid’s names for passwords. Change password on laptop/tablet/workstation every month. To create strong and unique password use some of the online TRUSTED password generators like Norton.Tip #4 Limit access to sensitive information
Set up a guest WIFI network if you have a lot of visitors at premises (like a restaurant) and limited access to your IT infrastructure. Use one network for employees, second for management and third for guests. Set password on all networks you and your staff are using.Tip #5 Don’t use private USB drives
Ban usage of private USB drives in the office. USB drives are usually infected by trojans or with similar malicious small apps that can spread all over the business network. Pictures, recent downloaded music or files from Torrent can seriously damage your network security.Tip #6 Use antivirus program
Install an anti-virus program on all computers in the office. It’s better to have any anti-virus app installed (even free versions) but to have nothing that will protect you. Try to regularly update virus base and keep the app up to date. Scan all your machines against viruses every month.Learn Why Cybersecurity is Important?

Best Server Antivirus
These are the best antivirus solutions for your server – recommended by our IT experts. Read all pros, cons and subscription plans.

13 Steps to Establish Business IT Security
If SMBs become affected by cyber threats, they are at risk of losing a lot of profit and reputation. Discover why your company may be at risk of cyberattacks.

Small Office Network Security Tips
Protect-Detect-React. To avoid risks and potential system jeopardizing, you need to make sure your cyber environment is protected with the latest network security tools.

10 Most Common Types of Cyber Attacks
It all started with ARPANET. Developed in the turmoil of the Cold War, ARPANET was the inception of the most fertile ground for any and every type of cyber-attacks imaginable. This was just the beginning…

Phishing in Details and How to Protect Your Self
Phishing or network identity theft is an attempt to steal data from Internet users through a fake site. Usually, such malicious website has offered by specially prepared e-mail or chat.

How to Prevent Man in The Middle Attack (MITM) Attack
MitM is the type of cyber-attack when hackers (attackers) intercept communication between two parties (usually user and application) and make way to modify that communication to collect valuable information.

DoS and DDoS Attacks and Prevention
State agencies, such as the N.S.A. and the Department of Homeland Security, are in charge of defending state networks. But, the private companies are left alone to protect themselves from the attacks of the DoS and his "more dangerous malware kid" DDoS.
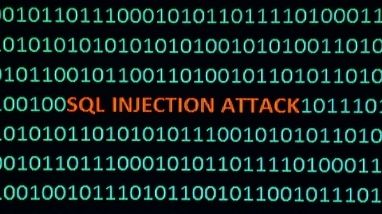
SQL Injection Attack 101
SQL injection is discovered more than 20 years ago and remains all these years as the potent malicious cyber-attack and require top database security priority.

Cross Scripting XSS Attack in Detail
Malicious scripts are frequently delivered in the bit forms of JavaScript code executed by the victim's browser, but exploits can involve malicious executable code in many different languages, such as Java, Ajax, Flash, VBScript, Active X, and HTML.