Phishing In Details and How to Protect Your Self
What is Phishing?
Phishing or network identity theft is an attempt to steal data from Internet users through a fake site. Usually, such malicious website has offered by specially prepared e-mail or chat. The sender thus instructs the victim to disclose confidential information via phone or the hyperlink in the email message. He uses this information for a variety of purposes, but most often to stealing money from a bank account or breaking into the victim's e-mail. In one sentence phishing is a technique for intercepting computer communications. It’s one of the earliest types of cyber-attacks, since the 1990s, and it’s still one of the most dangerous and widespread, with new phishing techniques becomes much more difficult for detecting.What Does Phishing Mean?
When you say "phish," it sounds same as a word fish. Similar as the fisherman throwing bait out there (the phishing email) and expecting that email recipient will bite. The term was created in the mid-1990 by the hackers to instruct AOL users to give them their login information. People who deal with this type of cybercrime are usually called “Scammers or Fraudsters"What is Phishing Site
Phishing site (“spoofed” site) is a site that attempts to steal personal user account data or other private info by fooling a user into convinced that he/her is on right URL. The user could even reach on a spoofed site by typing a wrong web address. The user must pay attention, regardless of the convincing appearance of the site. It's merely for fraudsters to create websites that mimic the genuine article, entirely with the logo and other graphics of the trusted website. The safest thing for the user if he isn't sure about a site, do not sign in. The best way to solve that situation is to close and reopen the browser, and then type the web address into the URL bar. Typing the exact web address is the ideal way to avoid a phishing site.
Generally, scammers attempt to fraud the user into providing private username and password so that they can access into an online account. When fraudsters get access, they can cause severe damage such as charge user credit cards, use personal information to commit theft, share private data or confidential private details and empty bank accounts. In the other word, they are capable to ruined somebody's life.
How to Prevent Phishing:
- False Company Name – Usually, the URL of a spoofed site seems correct but includes the typical misspelling of the company name or symbol or a character before or after the company name. Tricks with the replacement of letter l with number 1 are most common.
- Implementation of SSL Certificate – “HTTP://" at the start of the address on trusted company sign-in pages is wrong, the letter S must be included. Great majority of organization uses website with installed security certificate, meaning that the user should double-check the web site URL. It has to be “HTTP S ://"
- Watch out for Pop-Ups – the user should be cautious if he/she get redirect to the site that instantly displays a pop-up window demanding their username and password.
- Anti-Phishing Web Browsers – Great way to avoid spoofed sites is to use this type of browsers with suitable plug-ins that provide user to discover fraud.
- Use a Fake Password – If a website is not legitimate, the user mustn't use a real password to sign in. The user enters a fake a pass and appears to sign in, he or she is apparently on a spoofed site. The user must stops enter any more information and close a browser. But, some more sophisticated phishing sites instantly display an error message despite the password user enter. Even the password rejects, it's still not authentic.
- Carefully with other methods to detect an official site – Certain ways used to discover a safe location can't always be the right one. The locked padlock or small unbroken key at the left of the address bar doesn't mean that the user is on the correct web address. Only, because there is a lock or key and the security certificate appears legitimate, the user must be careful about the authenticity of that phishing site.
Warning: The best solution for the user is always to double-check the web address and looks carefully at whether there any irregularities.
What is Phishing Email
The phishing email is message designed to look authentic and usually imitate format used by the trusted company, including their logo and branding. It will redirect the user to a fake site, that appears like the legitimate, but has a little different URL. Example: If the official website is 'www.realbank.com,' the fraudster may use an address like 'www.rea 1 bank.com'.
How to Identify Phishing Email?
- Check, then Click – The user should place the mouse over any links embedded in the body of the email. If the link address appears suspicious, a user mustn't click on it. The best way is to open a new window and type the received link from the suspicions email directly in the URL bar.
- Inspect Spelling – Trusted company are very serious about email. Their emails typically don’t have spelling errors or bad grammar. The emails should be read cautiously and inform anything that looks illegally.
- Double-Check the Salutation – Is the message referred to an undetermined “Valued Customer?” If the email appears with that content, the user must be careful, since the trusted company’s procedural message starts with a personal addressing with users first and last name.
- Don’t Provide Personal Info – Legit banks and other enterprises will never require personal information by email. The user mustn't provide such kind of credentials to unsolicited emails.
- Analyze the Signature – A very little information about the signer or how a user can contact a company is undoubtedly a fraud. Legit companies always give contact info.
- Check the Attachments – Typically phishing method is an email with a pernicious attachment that contains malware or viruses. Malware can damage user data or files, use their passwords in illegal action or spy on them.
The 10 Most Common Email Phishing Subject
Phishing emails have based on the user's psychology. The scammers pretend as a person or organization with a high level of authority and calling on immediate action, and these emails are seriously convincing. The 10 most common headlines of these emails are:1. "Restart your Membership," 2. "Update your Official Record," 3. "Click to Learn More," 4. "You Missed a Delivery," 5. "Confirm Your Account," 6. "Your Account has been Locked," 7. "Suspended Account," 8. “Tax Refund”, 9. "Refund Due to System Error," 10. "Click to See your Revised Salary."
Types of Phishing
Here are 4 main types of phishing.Type #1 Deceptive Phishing
Deceptive phishing is the most often type of phishing attack, and it relates to an attack where the fraudster pretends to be a legit company and try to steal users personal and login information. The link de facto points to a scammers site with URL that practically identical to the authentic URL (usually one letter is out of order).- Example: User gets an email from a bank demanding that account has been frozen, user mustn’t click the link provided and enter account credentials.
Type #2 Spear Phishing
Spear phishing is a much more personalized tactic for phishers to get to the user. Scammers personalize their emails with username, position, company name, work phone number or other information that can find online (through company websites or social network platform), in an attempt to make user thinks that fraudsters have a connection with a user. Their mission is to trick a user into clicking a pernicious URL or an email attachment, which will provide them with personal user data. Experience says that the most efficiency spear phishing attacks are frequently the easiest and imitates the typical daily operational activities that might happen which occur during the working time.- Example: The user receives an email that's allegedly from user's organization HR department requesting a user to validate personal benefits policy data.
Type #3 Whale Phishing
Whale Phishing is when the fraudster successfully has spear phished a CEO or the other top executive of the organization and seceded to steal user's login data. The phisher then sends an email from the CEO account or creates a new domain name that's short by one letter or number and duplicates the CEO's info and demands that employee perform a wire transfer of funds to a financial institution of employee's choice. CEO attacks rarely set off common spam traps since they aren't mass email, the scammer deliberately chooses the victims.- Example: The user gets an email that's seemingly from top executive requesting from user to wire transfer the money, and to inform them when a user is available so they can send info of where it needs to go.
Type #4 Malware-Based Phishing
Malware-based phishing is when the phisher sends an email attachment or downloadable file to the user that uses the security gapes of the user’s device. When that attachment or file is click on, it starts dangerous software that’s been embed within attachment or file. Malware combine with computer viruses, ransomware, worms then runs on the user computer and spread to the others to infect them.- Example: The user can receive an email from an unknown person or organization requesting to download an invoice.
Office 365 Phishing Email
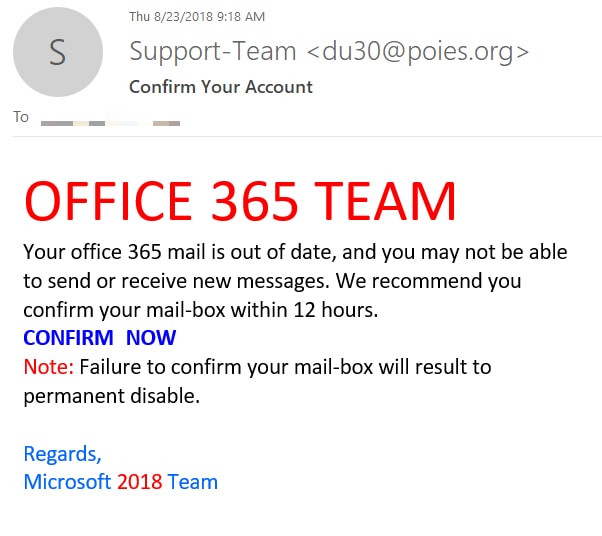
With the quick growth of Office 365, much more phishing attacks can occur within own infrastructure, primarily via email. The frequency of phishing inside Office 365 is supposed to cost the average company 1.3 compromised accounts every month. Still, phishing inside Office 365 isn’t the biggest problem for most organizations, but with fraudsters increasingly relying on sophisticated phishing tactics, it may become the biggest. That's why the users and network administrators must educate about ways to recognize this fraud.
Consider these signs:
- A warning that the user's computer is infected. The notification will automatically state call Windows support or contact Windows support, but it will rarely appear Microsoft support.
- The warning might be full screen or partial, but it will become problematic to close the window and to click the close button. It will not permit a user to exit from the popup.
- The user might hear previously prepared audio announcing the alert.
- Warning messages have detected on all browsers and operating system. User's pop-up blocker will not stop these alerts. The best way is to erase browser history after encountering one of these messages and track it with a virus scan and remove.
- The ideal defense is user education, necessary email filtering, and multi-factor authentication.
Secure your Business Today
Secure Networks ITC is reliable IT partner with 15+ year experience and undisputed Tech Support. Our team of technicians and engineers provide the best IT service in San Diego County.We have a various range of services that include phishing protection, anti-ransomware solutions and full protection of your computer network.
We partner with a IT corporation such as Dell, Microsoft, Cisco, Lenovo, VMware and Bitdefender. Contact us TODAY to get a best support against cyber-attacks and phishing protection.